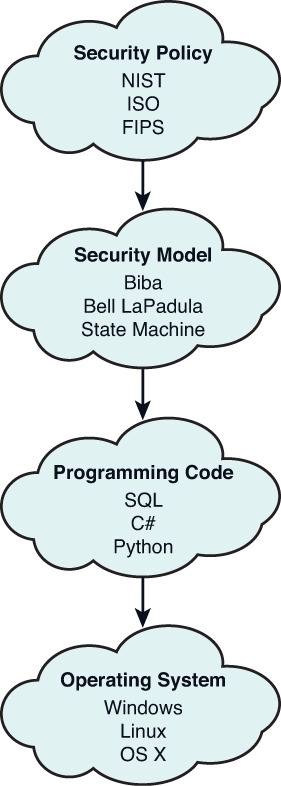
Discretionary Access Control vs Mandatory Access Control - Part 2: Mandatory Access Control Fundamentals
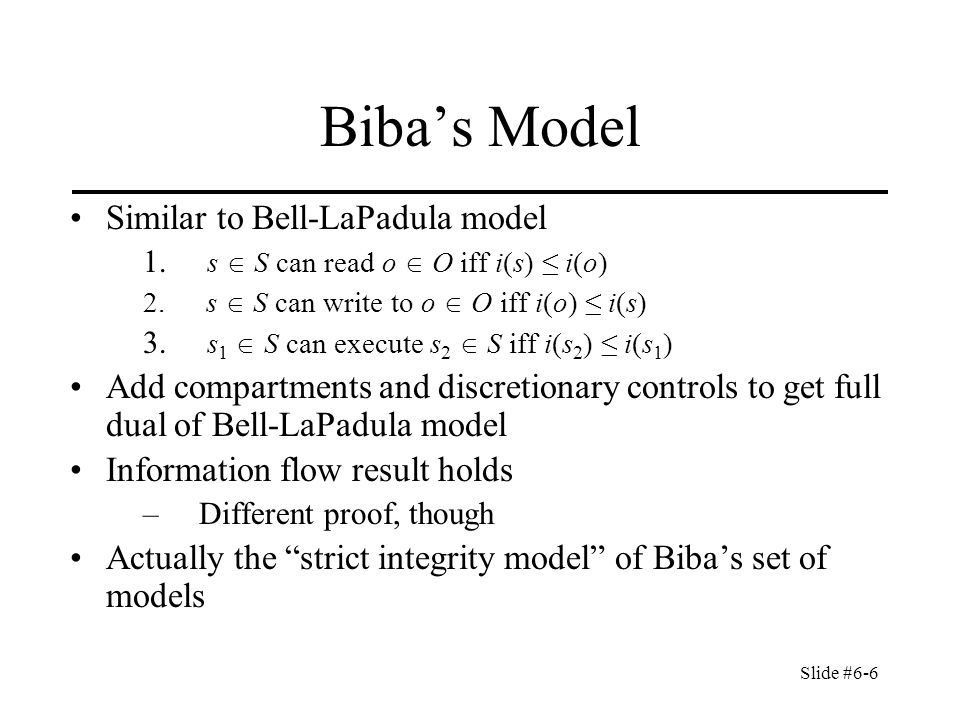
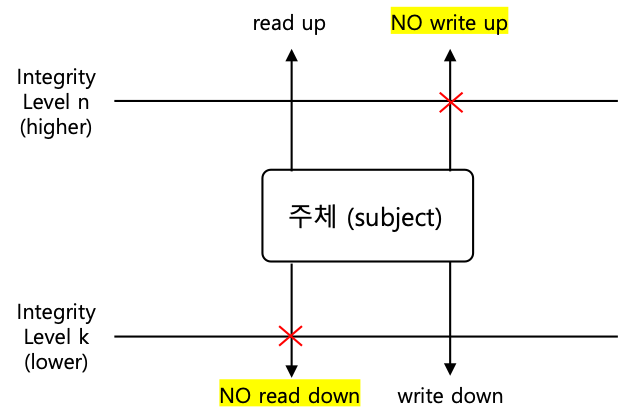
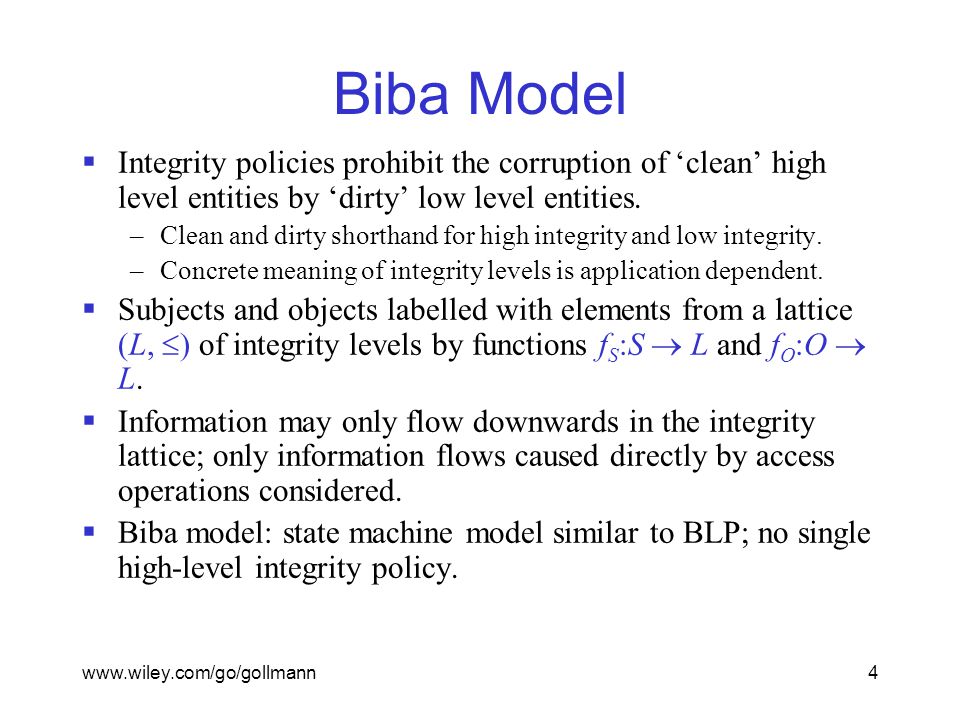
Integrity Models Biba Integrity Model (1977) Biba Model – ”no read down” Biba Model – ”no write up” Biba Model – i

Improved Biba model based on trusted computing - Liu - 2015 - Security and Communication Networks - Wiley Online Library

Figure 1 from Applying Dynamic Labels of the Biba Model in Forensic Evidence Analysis | Semantic Scholar